In my post earlier this week, I touched on a piece of the Content Security Policy header that is important to set correctly to prevent Cross Site Scripting (XSS) attacks. Today, I would like to talk about our Security Header Accelerator we have created to help our clients manage their Content Security Policy more efficiently.
Managing a website's Content Security Policy can be a bit of a tricky problem. For websites that run on the Microsoft .NET stack, this often involves manipulating the headers in the Web.Config file that is on the web server or cloud hosted infrastructure. Ideally, this is a file under software version control that is deployed in an automated manner. This allows for the content of the Web.Config to be transformed as appropriate across different environments. This strategy also allows sharing of values across environments where appropriate.
The Content Security Policy header is something that may need adjustment from time to time. A very common scenario where this occurs is when new marketing tag is added to the website via a tool such as Google Tag Manager, and that marketing tag is incompatible with the Content Security Policy. This prevents the marketing tag from working until your partner or development team can update the policy. This is an issue for organizations that are practicing agile marketing and constantly experimenting with new functionality.
To solve this problem, we moved the creation and definition of the security headers inside Sitecore's Content Editor interface.
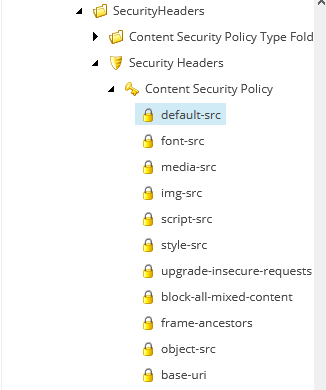
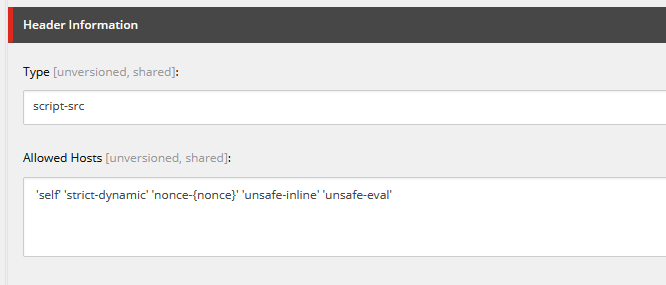
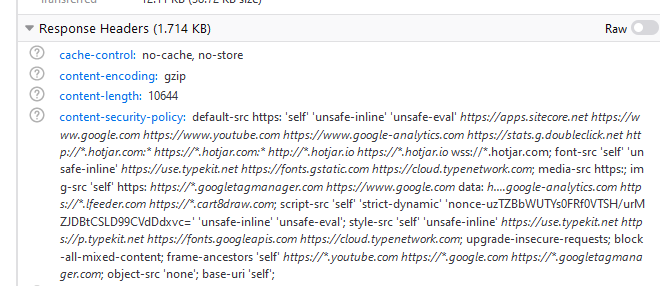
This accelerator allows our clients to modify the Content Security Policy to fit their needs and publish the changes just as changes to the website content are published. The Content Security Policy gets written to the response headers by the functionality, just like it would if it were managed in the Web.Config. It also solves the problems mentioned in my previous post regarding nonces and XSS attacks. The content editor can add the nonce to the script-src right from within Sitecore.
With this functionality, the Content Security Policy header is automatically appended to the response headers for visits to the site. This removes the need to change the value in the Web.Config.
Our accelerator works with multiple versions of Sitecore and is compatible with the Sitecore Experience Accelerator (SXA) Multi Site architecture.