LIBRARY
Ideas, strategies, and playbooks to help manufacturers and distributors win in digital: commerce, content, data, and beyond.
When Operations Outgrow ERP Workflows, Excel Quietly Becomes the Real System
Most organizations do not intentionally build operational systems in Excel. They emerge as workflows outgrow ERP flexibility and teams create spreadsheets to keep the business moving. Over time, those temporary fixes become critical operational layers powering pricing, reporting, product data, and day-to-day coordination across the business.
Digital Strategy
B2B Commerce
Governance

Building Agentic Product Discovery with SitecoreAI
SitecoreAI is far more interesting as an orchestration layer than a content generation feature. This article explores how adaptive product discovery can coordinate search, customer context, structured product data, and retrieval confidence in real time using Sitecore Search, CDP, XM Cloud, and AI-driven workflows. From hybrid retrieval pipelines to adaptive clarification and observability, the next generation of B2B commerce experiences will behave less like static catalogs and more like intelligent decision systems.
Sitecore
Site Search
AI

Why Wire & Cable Pricing Models Are Breaking in 2026
Wire and cable pricing models were built for stable markets. That assumption is breaking. Copper volatility, electrification demand, and supply pressure are exposing a deeper issue: pricing systems that cannot keep up with reality. The result is not just margin pressure. It is operational friction across quoting, sales, and customer trust.
Wire & Cable
Commergenix
Governance

From Cron Jobs to Workflow Engines: The Rise of Orchestration Layers
Most systems don’t fail because they can’t do the work. They fail because they can’t coordinate the work. As workflows span more systems and AI is layered into operations, orchestration becomes the control layer that determines whether anything runs reliably.
workflows
orchestration

Why Manufacturers Outgrow WordPress and WooCommerce
Most manufacturers start with WordPress and WooCommerce because they are fast, flexible, and good enough to get moving. But as digital maturity increases, the website stops being a marketing layer and starts becoming part of the business itself. That shift introduces complexity in pricing, product data, and integrations that loosely structured systems struggle to support. When manufacturers move beyond WooCommerce, it is not about chasing a better platform. It is a signal that their operations have outgrown the way their digital systems are structured.
B2B Commerce
Manufacturing

The Biggest Gap in B2B Shopify Isn’t Features. It’s Coherence
Shopify has made B2B ecommerce faster and more accessible than ever. But once you move beyond the storefront, most teams run into the same problem. The platform works, but the system around it does not. Pricing lives in one place, product data in another, and workflows in between. The result is not a feature gap. It is a coherence gap.
shopify
B2B Commerce
Digital Strategy

No Cookies, Still Regulated: The Reality of Ecommerce Analytics Under GDPR
Removing cookies does not remove your compliance obligations. If your ecommerce analytics is tied to known users, you are still processing personal data under GDPR. The real question is not how you track, but why and how your system is designed to use that data.
Privacy
B2B Commerce
GUIDE: Agentic Commerce Patterns
Agentic commerce is not a feature. It is a system. This guide breaks down the patterns that turn AI into something that can actually run your commerce operations.
AI
B2B Commerce
Guides & White Papers

Introducing the Product Truth SLA
Product data drives every transaction in B2B commerce, yet most organizations treat it as content instead of operational infrastructure. A Product Truth SLA establishes measurable standards for accuracy, completeness, and synchronization across ERP, PIM, ecommerce, EDI, and supplier systems. By mapping data flow upstream and enforcing service-level commitments around pricing, availability, lead time, and compliance attributes, manufacturers and distributors can prevent costly errors, protect margins, and build lasting customer trust.
B2B Commerce
Product Data
Agentic Commerce Is Not a Trend. It’s the Next Infrastructure Layer
The Agentic Commerce Protocol (ACP) is not a marketplace or a new checkout experience. It is infrastructure that standardizes how AI agents securely transact with merchant systems. As agent-driven purchasing scales, traditional ecommerce differentiation shifts away from page design and toward technical readiness, including clean product data, structured attributes, reliable APIs, and machine-readable pricing, availability, and constraints.
This article explains why agentic commerce is not optional for modern B2B organizations and what to do now to prepare, from auditing catalog quality to strengthening transactional reliability. The companies that adapt early will be the most discoverable and easiest for AI agents to buy from as this new layer between intent and transaction becomes normalized.
B2B Commerce
AI
Add EDI to Sitecore OrderCloud with n8n
A practical pattern for adding EDI to Sitecore OrderCloud using n8n with custom nodes: convert X12 to canonical JSON, validate it, automate a flow for 850/855 with 997 acknowledgments and observability.
Integration
B2B Commerce
Sitecore

When a Distributor’s ERP Knows the Truth but the Website Doesn’t
Even disciplined distributor environments experience breakdowns when ERP truth fails to propagate consistently across ecommerce, middleware, and order systems. ERP mismatch leads to manual intervention, pricing exposure, and fragile order flow. This post explains the technical patterns behind truth drift and how to reduce it.
Distribution
Product Data
Why Manufacturers Need Product Truth SLAs in 2026
Manufacturers already manage SLAs for shipping, quality, and service. In 2026, the bigger risk is information. Product Truth SLAs define how quickly manufacturers can detect changes, approve new truth, and publish it consistently across every channel that represents their brand.
Manufacturing
Product Data

When B2B eCommerce Breaks: How Manufacturers and Distributors Regain Control After a Digital Incident
When B2B eCommerce breaks, urgency replaces tolerance. This article explains how manufacturers and distributors regain control during active digital incidents.
B2B eCommerce

Universal Commerce Protocol (UCP): What Google and Shopify Just Introduced, and Why B2B Should Care
Google and Shopify have introduced the Universal Commerce Protocol (UCP), an emerging open-source effort designed to help AI agents and commerce systems work together more consistently. For B2B manufacturers and distributors, UCP is less about consumer checkout experiences and more about readiness. It signals a future where clean product data, clear pricing logic, strong identity controls, and resilient integrations determine how easily buyers and systems can transact at scale.
AI
B2B eCommerce

Normalize to Monetize: How AI Cleans Up Product Data for Manufacturers
Messy, inconsistent product data slows digital growth. This article shows how AI-driven taxonomy normalization helps manufacturers clean, structure, and monetize their data for scalable digital success.
AI
Product Data
Manufacturing
How Google AI Shopping’s Smarts Are Poised to Transform B2B Wholesale
Google AI Shopping, at the heart of AI Mode, isn't just a consumer-facing novelty. For B2B wholesalers, this evolution is a wake-up call. From AI-powered conversational search to real-time deal watching, Google is redefining product discovery with capabilities like query fan-out, agentic checkout, and virtual try-on. In a world where procurement teams expect quick, precise results, wholesalers need to rethink how they feed data into Google’s ecosystem before AI decides which supplier gets the order.
B2B eCommerce
AI
Manufacturers and the Channel Conflict Dilemma
Channel conflict occurs when manufacturers’ DTC sales overlap with distributor or retailer channels. Learn how to manage pricing, partnerships, and regions to minimize risk and maximize opportunity.
Manufacturing
DTC

How Solr and Elasticsearch Calculate Search Results: A Guide for B2B and Wholesale eCommerce
B2B eCommerce platforms rely on Solr and Elasticsearch to power search, but how do they actually work? Learn how indexing and scoring impact what your buyers see and why it matters.
Site Search
B2B eCommerce

Comparing Enterprise DAM Platforms: Sitecore Content Hub, Frontify, Bynder, and More
Modern DAM platforms are no longer just repositories for marketing assets. They have become operational systems that govern workflows, product content, AI-assisted metadata, brand consistency, and omnichannel content delivery. This article compares leading DAM platforms including Sitecore Content Hub, Frontify, Bynder, Optimizely DAM, and Adobe Experience Manager Assets through the lens of enterprise governance, workflow orchestration, AI capabilities, and real-world operational fit.
B2B Commerce
Product Data
Digital Strategy

Beyond GA4: The Best Google Analytics Alternatives for B2B eCommerce in 2025
GA4 left many B2B teams frustrated. This article highlights the best analytics alternatives for manufacturers and distributors, from lightweight privacy-first tools to enterprise-grade solutions.
B2B eCommerce
Digital Strategy

The Hidden Metric That Transforms Your B2B Ecommerce Search Experience
Search Effectiveness Rate reflects how often your eCommerce site delivers relevant results. For B2B buyers dealing with complex catalogs, a strong search experience is essential. Learn how to track and improve this key performance indicator.
B2B eCommerce
Site Search
KPI

Orderability Data: EDI+API Exception-Proofing as a Revenue Lever
Orderability data is the missing layer between product content and revenue through distributors. Learn how structured ordering semantics plus EDI+API exception-proofing reduces friction and accelerates sell-through.
Manufacturers
B2B eCommerce
Integrations

From Spreadsheets to Strategy: When It’s Time for a PIM in B2B Commerce
Product data chaos slows digital growth. See when B2B manufacturers and distributors should implement a PIM to turn messy spreadsheets into structured, revenue-driving strategy.
B2B eCommerce
PIM
GUIDE: Mastering B2B eCommerce Search
Learn how B2B buyers search and how to improve relevance, product data, and UX. Download Layer One’s free guide to create a smarter, higher-converting site search experience.
Guides & White Papers

The Ecommerce Maturity Gap in Wire & Cable Is No Longer Subtle
Ecommerce in wire and cable is no longer a question of presence. It is a question of usability. As 2024 closes, fragmented product data, manual quoting, and rigid pricing systems are creating a visible maturity gap between companies that can operate at scale and those that cannot.
Wire & Cable
B2B Commerce
Why Programmatic Pricing, Availability, and Constraints Matter in B2B Ecommerce
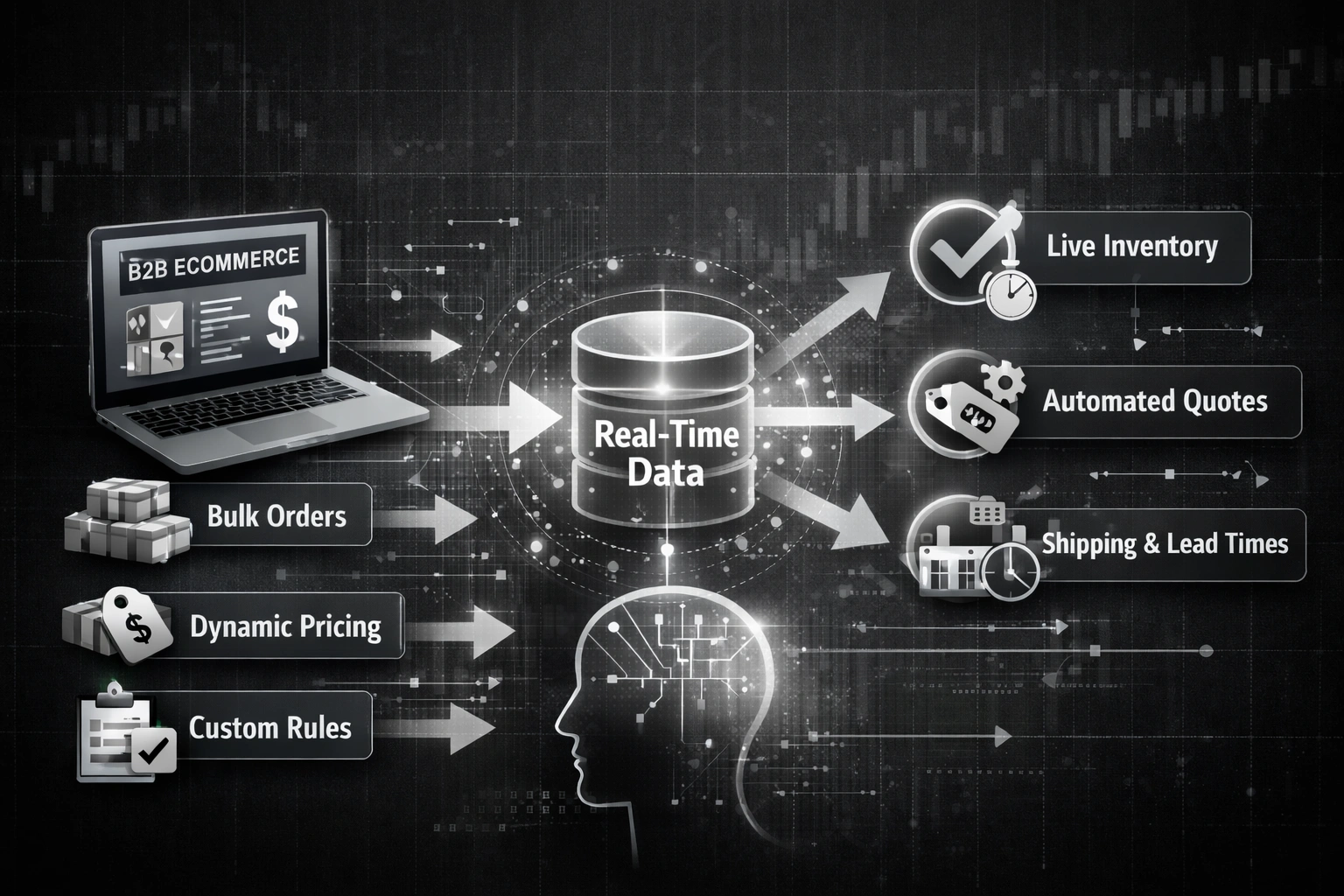
In B2B ecommerce, pricing, availability, and constraints are not just fields on a product record. They are the programmatic promises your business makes to buyers and the systems that buy on their behalf. When those signals are inconsistent across web, APIs, punchout, and EDI, the fallout shows up as misquotes, backorders, order holds, and expensive manual exception handling.
This article explains why manufacturers should treat these three signals as a unified “orderability” decision, exposed deterministically and with traceability. You will learn how a simple Orderability Contract helps align channels, reduce disputes, and make self-service buying reliable at scale.
B2B Commerce
Product Data

How to Convert EDI Documents to JSON in Node.js (X12 or EDIFACT)
A practical implementation guide for converting X12 or EDIFACT EDI documents into usable JSON in Node.js: parsing strategies, canonical schemas, validation with AJV, testing fixtures, and production observability.
Integration
B2B eCommerce

As Contractors Consolidate Do Relationships Matter
Private equity is transforming HVAC, plumbing, and electrical contractors into data-driven operations. As relationships give way to digital optimization, distributors must adapt to stay relevant.
B2B eCommerce
Digital Strategy

Why are we just doing this now?
Many distributors hesitate to start eCommerce transformation until they “feel ready.” The truth? Waiting costs more. Learn why bringing in a consultative partner now is the key to long-term success.
Digital Strategy
B2B eCommerce

Healthy Site Search is Business Critical
B2B buyers rely on search to find products fast. Learn why weak search experiences cost sales, how top distributors are improving, and what steps to take to strengthen your site’s performance.
Site Search
14 Focus Points

VIDEO: Beth Ladd From ASA at ASA Network 23
We talk with Beth Ladd about all the exciting things coming out of ASA including product data transfer between Manufacturers and Distributors.
Video
ASA

What is Search Intent in B2B eCommerce?
Search intent explains what a buyer really means when they type in your search bar. See how browse, implicit, and explicit intent reduce bounces and increase conversions in B2B eCommerce.
Site Search
14 Focus Points

VIDEO: Dean Mueller From DSG at ASA Network 23
We Talk to Distribution Expert Dean Mueller from DSG.
Video
ASA

Helping Clients with Product Data
Learn how Layer One helps clients enhance product data quality, from taxonomy and brand pages to ERP integration, improving eCommerce performance and customer experience.
Product Data
14 Focus Points

VIDEO: ASA Network 23 Recap
See interviews and insights from ASA Network 23 in Orlando.
Video
ASA

Are we at a Disruption Point for Distribution?
Online sales are growing while traditional distribution lags behind. Layer One CEO Chad Albrecht shares insights on why PHCP distributors face a digital disruption point, and what it takes to compete.
B2B eCommerce
Digital Strategy

Ecommerce Onboarding (Focus Pt. 7)
Getting wholesale customers to order online takes more than a great platform. Learn seven proven strategies to increase eCommerce adoption and boost digital order volume.
14 Focus Points
B2B eCommerce

DSG Guest Post: Are You Getting the Most from Your eCommerce Solution Partner?
Distributors succeed when their eCommerce partner acts as a consultative advisor, not just an implementor. Learn how to assess your current partnership and find one that drives measurable growth.
B2B eCommerce

Growth KPIs (Focus Pt. 6)
Smart growth in B2B eCommerce requires tracking the right KPIs. Learn the nine most impactful metrics, from CLV to search effectiveness, that uncover what’s working and what’s not.
14 Focus Points
B2B eCommerce

Auto Sync Product Data Feeds to PIM
Manual product data imports waste time and create errors. This guide shows how to auto-sync AD, Syndigo, 1WorldSync, and DDS feeds into PIMs like inriver, with a real client example and config snippets you can adapt.
Product Data
B2B eCommerce

User Experience (Focus Pt. 5)
A high-performing B2B eCommerce site requires more than design. Explore how navigation, search, personalization, and responsive design create the UX modern buyers expect.
14 Focus Points
UX

Optimizely Performance and Stability
A fast, reliable Optimizely site is essential for B2B success. Explore five common performance issues, jobs, fragile UI, APIs, databases, and scaling, and how to fix them for better results.
B2B eCommerce
Optimizely

Empower Search (Focus Pt. 4)
Poor site search costs B2B companies sales. Learn seven actionable ways to improve findability, optimize product data, and build a smarter search that drives revenue and customer trust.
14 Focus Points
Site Search

Product Data Quality (Focus Pt. 3)
Product data quality determines how easily customers find, understand, and buy from you. Learn how to improve accuracy, completeness, and findability to boost B2B eCommerce performance.
14 Focus Points
Product Data

Iterative Thinking (Focus Pt. 2)
Iterative thinking helps B2B organizations refine digital strategies through rapid feedback and improvement. Learn how applying the PDCA cycle strengthens eCommerce, marketing, and customer experience.
14 Focus Points

Site Performance/Stability (Focus Pt.1)
Site stability and performance are business-critical for B2B eCommerce. Learn how reliability and speed affect SEO, conversions, and customer trust, and how to optimize them for success.
14 Focus Points

Distributor eCommerce Now 20 Percent of Sales and Accelerating
Predictions of a post-COVID slump in online usage didn’t materialize for distributors. Instead, all those folks who got used to buying online when they didn’t have a choice have embraced the channel and – apparently – talked their coworkers into joining the digital customer club.
B2B eCommerce
Digital Strategy

The Future of HVAC: Attending the 2023 Auer Expo
Attending the Auer Expo was a fantastic experience that provided insights into the latest developments in the HVAC industry. The event brought together a diverse group of engineers, dealers, industry experts, and manufacturers from around the world, creating a vibrant atmosphere for learning and networking.
B2B eCommerce
Digital Strategy

What Engineers Want from a Manufacturer’s Website
The B2B buying market has changed radically for almost all professions, and engineers are no exception. Here's what engineers said they wanted in their shopping experience, and what may happen if companies don't adapt.
Digital Strategy
B2B eCommerce
WHITE PAPER: 4 Keys to Attracting Engineers to Manufacturer Websites
Engineers now expect manufacturer websites to provide fast access to deep technical content, intuitive navigation, and tools that support their design and specification work. This guide shares research from nearly 300 engineers and outlines four essential improvements manufacturers can make to attract engineers, strengthen trust, and increase product specification.
Guides & White Papers

Personalization in B2B eCommerce
B2B buying is complex and involves various departments, all while customers want to minimize the time and effort it takes to make purchasing decisions. Learn how to understand your customer on a deeper level using the right data for B2B, B2C, and B2X buyers alike.
Digital Strategy
B2B eCommerce

Processing JSONL
Quick demonstration of JSONL, a data format that is appearing in more and more systems.
SOFTWARE ARCHITECTURE

The Pitfalls of JavaScript Libraries
JavaScript libraries have revolutionized web development by providing developers with powerful tools, frameworks, and pre-built components to expedite the creation of interactive and feature-rich web applications. However, a growing trend of incorporating an excessive number of JavaScript libraries into projects can introduce pitfalls that developers need to be mindful of.
User Experience
SOFTWARE ARCHITECTURE

Dazzlingly Easy Sitecore Content Comparison with Razl
This post introduces a tool called Razl, which is very helpful in moving Sitecore items between environments.
Sitecore

What you need to know about event driven architecture
There are many architectures available to the development teams; in this post we take a look at event driven architecture. Whether building a new system or maintaining an existing system, we'll examine the basic components and the benefits of the design.
SOFTWARE ARCHITECTURE

The Differences Between JSS React Developer Modes
With multiple development modes available, we review the pros and cons to working in disconnected, connected, or integrated mode.
Sitecore

Getting final Sitecore configurations anywhere, anytime, with Sitecore ConfigBuilder
Sometimes you need access to the final Sitecore configuration file, but you can't make use of ShowConfig.aspx
Sitecore

Providing Content Customization
Content Authors deserve more flexibility. Here is how we provide a more dynamic experience.
User Experience
Umbraco
Sitecore

Creating Your First JSS React Application
A step by step guide laying the foundation to building your first Sitecore JSS React application.
Sitecore

Content Security Policy Management in Sitecore
Our new Security Header Accelerator allows marketers to run experiments with an agile mindset more easily.
Sitecore

Prevent XSS Attacks with a Nonce in the Content Security Policy
Cross Site Scripting attacks can be a danger to visitors of your website. This post explains how to prevent them using a nonce in your Content Security Policy.
Security

Screencast - Triggering Marketing Automation Campaigns
Sitecore's Marketing Automation engine is a powerful tool in your toolbox. We will cover how to trigger an automation campaign in this screencast.
Sitecore
Video

Screencast - Installing Sitecore Forms Extensions
Sitecore Forms Extensions allows for 9.0 - 9.3 Sitecore customers to quickly capture xDB contacts. This screencast covers how to install Sitecore Forms Extensions and configure your first form to capture the data.
Sitecore
Video

Screencast - How to Publish a Sitecore Form
Sitecore Forms is a powerful WYSIWYG form editing tool. This video covers the flow to publish a Sitecore Form.
Sitecore
Video

Screencast - Introduction to SXA Rendering Variants
SXA Rendering Variants allow for rapid, iterative development. Learn more about Rendering Variants in this screencast.
Sitecore
Video

Webinar - Strategies for Maturing Your Ecommerce Experience
Navigating the commerce space is harder today than it has ever been. How do you know where you are compared to your peers? What is a logical next step? How much will it cost? In this webinar your hosts from Layer One and Sitecore will begin to answer these questions for you.
Digital Strategy
Sitecore
B2B eCommerce

HTTP Header Series: Feature-Policy
In our opening to this series, we discussed some of the reasons for Security Headers. In this post we will describe in more detail the (currently experimental) Feature-Policy header which provides a mechanism to allow and deny the use of browser features.
Security

HTTP Header Series: Referrer-Policy
In our opening to this series, we discussed some of the reasons for Security Headers. In this post we will describe in more detail the Referrer-Policy header which controls how much information is sent in the Referrer HTTP header.
Security

HTTP Header Series: Content-Security-Policy
In our opening to this series, we discussed some of the reasons for Security Headers. In this post we will describe in more detail the Content-Security-Policy header that allows web site administrators to control resources the user agent is allowed to load for a given page. This header is critical is defending against cross-site scripting attacks.
Security

The Battle Between Page Speed and Google Tag Manager
While GTM itself loads asynchronously, the tags it manages can still compete with core content during the most performance-sensitive phase of page load. By separating essential tracking from scripts that can wait and triggering those deferred tags with a custom afterload event, teams can reduce browser workload, protect Core Web Vitals, and improve user experience without sacrificing valuable analytics or marketing data.
SEO
Guides & White Papers

Four things you wanted to know about Sitecore JavaScript Services
There are lots of great reasons to choose a Sitecore JSS site. From a software development perspective, Sitecore JSS embraces the most modern development practices and paradigms.
Sitecore

HTTP Header Series: The "Xs"
In our opening to this series, we discussed some of the reasons for Security Headers. In this post we will describe in more detail some of the security headers that still bear the “X” prefix
Security

HTTP Header Series: HTTP Strict Transport Security
In our opening to this series, we discussed some of the reasons for Security Headers. In this post we will describe in more detail the need for the HSTS header.
Security

HTTP Header Series: Security Headers
Understand how defining these HTTP headers can help reduce your site vulnerability and make the user experience more secure.
Optimizely
Sitecore
Umbraco

The European General Data Protection Regulation Change Is The Biggest Since 1995
Layer One Media’s clients do business worldwide. As such, they are constantly collecting data on their customers and website visitors. Recently, the EU and Parliament adopted new regulations that will not only effect third party cloud providers but the companies that collect data as well. Following is a bulletin we think you’ll find helpful in preparing for the change.
Digital Strategy

Sitecore Commerce Accelerator leverages Sitecore Commerce
Sitecore Commerce is ready for manufacturers and distributors. We've pre-built the features most B2Bs are looking for Multi-Featured Homepage and search, Multiple Payment Processing Options, Welcome and View Personalization, Product Category, Listing and Detail,Cross-Sell, Up-Sell products and more!
Sitecore

Configuring Dependency Injection in Umbraco
This webinar will explore pre-sales, sales and post sales personalization tactics that will make your company easier to do business with and build digital brand loyalty.
Umbraco

Decreasing Umbraco Feature Development Time with Models Builder
ModelsBuilder is a tool that is built into the Umbraco platform since version 7.4. What it does is allow the development team to use the Umbraco back office to define the necessary document types for a feature. Then the tool will generate the files necessary for the developer to begin interacting with the document types in the code.
Umbraco

Why is B2B Commerce so difficult?
Manufacturers and Distributors are hearing the call from their customers – “lower costs and be easier to do business with!” For most, this means providing a streamlined digital commerce experience from relevant information to fulfillment and post-sales support. So what do I keep hearing from manufacturers as to why B2B digital commerce is so hard?
B2B eCommerce
Digital Strategy

4 Key Considerations for Integrations
Creating meaningful integration is where the distinction between creating business value and busywork lies. Poor integration adds to maintenance, may cause your site to load slowly and more to keep track of in the long term. So, the question becomes: how do you determine what provides the most meaningful business value that becomes most useful to integrate with?
Digital Strategy

Managing Channel Conflict with Extended Supply
Since the early 90s, the trend in mid and large size B2B companies has been to consolidate their decentralized procurement groups and streamline their supply chain operations optimizing their buying power, supplier relationships and of course, reduce cost. This optimization typically lends to procurement groups purchasing product and services for multiple ship-to locations.
B2B eCommerce
Digital Strategy

Post-Sales: B2B Digital “Ease of Doing Business”
In the second post, we reviewed digital pre-sales for digitally servicing your customers and the third focused on sales phase. As the fourth and final in a four-part series, we will review the critical post-sales phase for Digitally servicing B2B Customers.
B2B eCommerce

All about the Sitecore Commerce Profile System
The Sitecore Commerce profile system is one of the remaining legacy Commerce Server sub-systems, and like the other Sitecore Commerce systems is incredibly flexible but somewhat complicated. This post will give you the run down on the what, how and why so you can familiarize yourself with designing or developing against the system.
UX
B2B eCommerce
Sitecore

Sitecore Personalization - Why and How
Why is personalization so important? Simple, you want to provide the best possible experience to your prospect or customer. This is absolutely critical. You want every interaction with your customer to be as effective and efficient as possible, this requires at least a certain amount of knowledge of your customer but obviously, you can never have too much data from which to make decisions.
UX
Sitecore
Digital Strategy

Five things you wanted to know about Sitecore Commerce
Is your organization thinking about the new release of Sitecore Commerce announced at the National Retail Federation show earlier this year? It doesn’t matter if you are in the world of B2B or B2C, online commerce platforms are significant in myriad ways to businesses and that is why Sitecore has invested so heavily in the platform. As one of the 19 Global Sitecore Commerce MVP’s, I’d like to take a moment to answer some of the top-level questions that people often have about the platform.
B2B eCommerce
Sitecore

Converting B2B Customers through Digital Sales Services
As the third in a four-part series, I want to discuss delivering sales phase capabilities involved with the “Being-Serviced” B2B Customer. In the first post, I introduced the “Being-Serviced” B2B Customer as those that will have matured beyond requiring superior “Self-Service” capabilities to those that will want to “Be-Serviced”. Understanding what this means within your industry, to your Partners and End Customers will be critical.
B2B eCommerce
UX

Marketing Analytics and Measurement Approach
Collecting metrics is easy. Knowing which ones matter is harder. This article walks through how B2B companies can align goals, KPIs, and analytics tools to create a measurement plan that drives real business outcomes.
Digital Strategy

Pre-Sales Servicing of B2B Customers
B2B buyers often make decisions online before sales ever gets involved. This article explores how manufacturers and distributors can deliver digital pre-sales servicing that influences buying decisions.
B2B eCommerce
Digital Strategy
UX

Hosting Sitecore in Azure: A guide to the basics
Thinking about hosting Sitecore in Microsoft Azure? This guide explains the differences between IaaS and PaaS hosting models, their pros and cons, and what they mean for your Sitecore environment.
Sitecore

Beyond Self Service in the B2B world
Self-service in B2B is now table stakes. The next competitive advantage comes from creating "being serviced" experiences—personalized, value-added interactions that build trust and long-term loyalty.
B2B eCommerce

Avoiding Marketplace Commoditization
B2B marketplaces can erode margins and commoditize products. This article explains how manufacturers can avoid the trap and win with value-added services, stronger channel support, and better digital experiences.
Digital Strategy

B2B eCommerce Success the “First Time”
B2B eCommerce is now a necessity. This article outlines 10 keys manufacturers and distributors should follow to ensure their first eCommerce initiative succeeds.
B2B eCommerce

The EU, GDPR and Umbraco CMS
GDPR reshaped how businesses handle data privacy. This article explores what the regulation means for manufacturers and distributors, and how Umbraco CMS can support compliance efforts.
Digital Strategy
Umbraco

Pardot Engagement Studio
Pardot’s Engagement Studio gives B2B marketers a visual, flexible way to design nurture campaigns. For manufacturers and distributors, it means smarter targeting, clearer reporting, and better alignment with sales.
Marketing

Sitecore & hCard Microformat
Sitecore can mis-handle tel: links in General Link fields by injecting http://. This article shows a quick pipeline fix and how to implement hCard/h-Card microformats to improve compatibility and SEO.
Sitecore

Personas, Profiles & Scoring Models: Marketing Automation
Personas and profiles help you understand buyers, but scoring models show you who is ready to engage. Here’s how manufacturers and distributors can use all three in marketing automation.
Digital Strategy
B2B eCommerce

1:1 Marketing
Batch-and-blast is dead. Learn how manufacturers and distributors can use 1:1 marketing nurture paths to deliver relevant content, personalize engagement, and create sales-ready leads.
Marketing

Prep Your Website For Marketing Automation
Marketing automation works only if your website is ready. This article explains how manufacturers and distributors can optimize forms, integrate with platforms, and implement tracking to fuel campaigns.-->
Marketing

The Four Stages of Marketing Automation
Marketing automation maturity happens in stages. This article outlines the journey from skepticism to advanced 1:1 innovators, helping manufacturers and distributors see what’s next on their path.
Marketing

Is There ROI for Marketing Automation?
Marketing automation creates momentum, but executives want proof. This article explains directional ROI and account-based ROI so manufacturers and distributors can measure impact with confidence.
Marketing

What's on your Digital Marketing Roadmap?
A digital marketing roadmap connects platforms, processes, and strategy. Learn how to start simple, avoid perfection paralysis, and create a 2–3 year plan for marketing automation growth.
Marketing

The Top Three Segmentation FYI's For Marketing Automation
Strong segmentation is the difference between opt-outs and conversions. This article highlights three practical tips to improve your email marketing automation and keep prospects engaged.
Marketing

10 B2B eCommerce Strategy Considerations
eCommerce is never “done.” This article outlines 10 essential considerations for manufacturers and distributors to keep their B2B eCommerce strategies current and competitive.
B2B eCommerce
Digital Strategy

MDM or PIM for B2B?
Poor product data holds back B2B eCommerce. This article explains the differences between MDM and PIM, their roles in product data quality, and how manufacturers and distributors should decide between them.
Product Data